Find all running hosts / used IPs on your local wireless or ethernet network
If you're using a Free Software OS such as GNU / Linux or some other proprietary OS such as Mac OS X or Windows and you need a quick way to check all running IPs hosts / nodes locally on your current connected Ethernet or Wireless network, here is how to do it with nmap (Network exploration and security tool port scanner).
So why would you do scan that?
Well just for fun, out of curiousity or just because you want to inspect your local network whether someone unexpected cracker did not break and is not using your Wi-Fi or Ethernet local network and badly snoring your network listening for passwords.
Before you start you should have installed NMAP network scanner on your GNU / Linux, to do so on
Redhat Based Linux (Fedora / CentOS / Redhat Enterprise RHEL):
yum -y install nmap
…
On Deb based GNU / Linux-es such as Ubuntu / Mint / Debian etc.
apt-get install –yes nmap
…
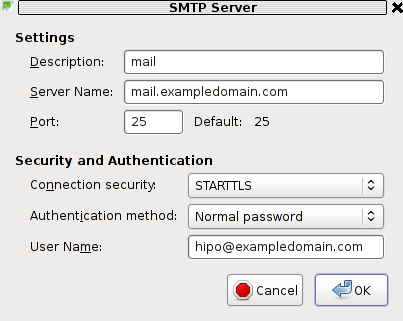
To install nmap on FreeBSD / NetBSD / OpenBSD OS issue from console or terminal:
cd /usr/ports/security/nmap
make install clean
…
or if you prefer to install it from latest binary instead of compiling
pkg_add -vr nmap
…
On a proprietary Mac OS X (I don't recommend you to use this obnoxious OS which is designed as a proprpietary software to steal your freedom and control you, but anyways for Mac OS victims), you can do it to with Macs equivalent tool of apt-get / yum called homebrew:
Open Mac OS X terminal and to install homebrew run:
ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)"
brew install nmap
brew search nmap
brew info nmap
If you want to do it system wide become root (super user) from Mac terminal with
su root
and run above commands as administrator user.
Windows users might take a look at Nmap for Windows or use the M$ Windows native portqry command line port scanner
Test whether nmap is properly installed and ready to use with command:
nmap –help
Nmap 6.00 ( http://nmap.org )
Usage: nmap [Scan Type(s)] [Options] {target specification}
TARGET SPECIFICATION:
Can pass hostnames, IP addresses, networks, etc.
Ex: scanme.nmap.org, microsoft.com/24, 192.168.0.1; 10.0.0-255.1-254
-iL <inputfilename>: Input from list of hosts/networks
-iR <num hosts>: Choose random targets
–exclude <host1[,host2][,host3],…>: Exclude hosts/networks
–excludefile <exclude_file>: Exclude list from file
HOST DISCOVERY:
-sL: List Scan – simply list targets to scan
-sn: Ping Scan – disable port scan
-Pn: Treat all hosts as online — skip host discovery
-PS/PA/PU/PY[portlist]: TCP SYN/ACK, UDP or SCTP discovery to given ports
-PE/PP/PM: ICMP echo, timestamp, and netmask request discovery probes
-PO[protocol list]: IP Protocol Ping
-n/-R: Never do DNS resolution/Always resolve [default: sometimes]
–dns-servers <serv1[,serv2],…>: Specify custom DNS servers
–system-dns: Use OS's DNS resolver
–traceroute: Trace hop path to each host
SCAN TECHNIQUES:
-sS/sT/sA/sW/sM: TCP SYN/Connect()/ACK/Window/Maimon scans
-sU: UDP Scan
-sN/sF/sX: TCP Null, FIN, and Xmas scans
–scanflags <flags>: Customize TCP scan flags
-sI <zombie host[:probeport]>: Idle scan
-sY/sZ: SCTP INIT/COOKIE-ECHO scans
-sO: IP protocol scan
-b <FTP relay host>: FTP bounce scan
PORT SPECIFICATION AND SCAN ORDER:
-p <port ranges>: Only scan specified ports
Ex: -p22; -p1-65535; -p U:53,111,137,T:21-25,80,139,8080,S:9
-F: Fast mode – Scan fewer ports than the default scan
-r: Scan ports consecutively – don't randomize
–top-ports <number>: Scan <number> most common ports
–port-ratio <ratio>: Scan ports more common than <ratio>
SERVICE/VERSION DETECTION:
-sV: Probe open ports to determine service/version info
–version-intensity <level>: Set from 0 (light) to 9 (try all probes)
–version-light: Limit to most likely probes (intensity 2)
–version-all: Try every single probe (intensity 9)
–version-trace: Show detailed version scan activity (for debugging)
SCRIPT SCAN:
-sC: equivalent to –script=default
–script=<Lua scripts>: <Lua scripts> is a comma separated list of
directories, script-files or script-categories
–script-args=<n1=v1,[n2=v2,…]>: provide arguments to scripts
–script-args-file=filename: provide NSE script args in a file
–script-trace: Show all data sent and received
–script-updatedb: Update the script database.
–script-help=<Lua scripts>: Show help about scripts.
<Lua scripts> is a comma separted list of script-files or
script-categories.
OS DETECTION:
-O: Enable OS detection
–osscan-limit: Limit OS detection to promising targets
–osscan-guess: Guess OS more aggressively
TIMING AND PERFORMANCE:
Options which take <time> are in seconds, or append 'ms' (milliseconds),
's' (seconds), 'm' (minutes), or 'h' (hours) to the value (e.g. 30m).
-T<0-5>: Set timing template (higher is faster)
–min-hostgroup/max-hostgroup <size>: Parallel host scan group sizes
–min-parallelism/max-parallelism <numprobes>: Probe parallelization
–min-rtt-timeout/max-rtt-timeout/initial-rtt-timeout <time>: Specifies
probe round trip time.
–max-retries <tries>: Caps number of port scan probe retransmissions.
–host-timeout <time>: Give up on target after this long
–scan-delay/–max-scan-delay <time>: Adjust delay between probes
–min-rate <number>: Send packets no slower than <number> per second
–max-rate <number>: Send packets no faster than <number> per second
FIREWALL/IDS EVASION AND SPOOFING:
-f; –mtu <val>: fragment packets (optionally w/given MTU)
-D <decoy1,decoy2[,ME],…>: Cloak a scan with decoys
-S <IP_Address>: Spoof source address
-e <iface>: Use specified interface
-g/–source-port <portnum>: Use given port number
–data-length <num>: Append random data to sent packets
–ip-options <options>: Send packets with specified ip options
–ttl <val>: Set IP time-to-live field
–spoof-mac <mac address/prefix/vendor name>: Spoof your MAC address
–badsum: Send packets with a bogus TCP/UDP/SCTP checksum
OUTPUT:
-oN/-oX/-oS/-oG <file>: Output scan in normal, XML, s|<rIpt kIddi3,
and Grepable format, respectively, to the given filename.
-oA <basename>: Output in the three major formats at once
-v: Increase verbosity level (use -vv or more for greater effect)
-d: Increase debugging level (use -dd or more for greater effect)
–reason: Display the reason a port is in a particular state
–open: Only show open (or possibly open) ports
–packet-trace: Show all packets sent and received
–iflist: Print host interfaces and routes (for debugging)
–log-errors: Log errors/warnings to the normal-format output file
–append-output: Append to rather than clobber specified output files
–resume <filename>: Resume an aborted scan
–stylesheet <path/URL>: XSL stylesheet to transform XML output to HTML
–webxml: Reference stylesheet from Nmap.Org for more portable XML
–no-stylesheet: Prevent associating of XSL stylesheet w/XML output
MISC:
-6: Enable IPv6 scanning
-A: Enable OS detection, version detection, script scanning, and traceroute
–datadir <dirname>: Specify custom Nmap data file location
–send-eth/–send-ip: Send using raw ethernet frames or IP packets
–privileged: Assume that the user is fully privileged
–unprivileged: Assume the user lacks raw socket privileges
-V: Print version number
-h: Print this help summary page.
EXAMPLES:
nmap -v -A scanme.nmap.org
nmap -v -sn 192.168.0.0/16 10.0.0.0/8
nmap -v -iR 10000 -Pn -p 80
SEE THE MAN PAGE (http://nmap.org/book/man.html) FOR MORE OPTIONS AND EXAMPLES
Most local router local networks are running under an IP range of 192.168.0.1/24 (192.168.0.1.254) or 192.168.1.1/24 or at some weird occasions depending on how the router is configured it might be something like 192.168.10.0/24 to be sure on what kind of network your computer is configured, you can check with ifconfig command, what kind of network IP has the router assigned to your computer, here is output from my Debian GNU / Linux /sbin/ifconfig
hipo@noah:~$ /sbin/ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:336 errors:0 dropped:0 overruns:0 frame:0
TX packets:336 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:26656 (26.0 KiB) TX bytes:26656 (26.0 KiB)
wlan0 Link encap:Ethernet HWaddr 00:1c:bf:bd:27:59
inet addr:192.168.0.103 Bcast:192.168.0.255 Mask:255.255.255.0
inet6 addr: fe80::21c:bfff:ffbd:2759/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:112836 errors:0 dropped:0 overruns:0 frame:0
TX packets:55363 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:141318655 (134.7 MiB) TX bytes:7391330 (7.0 MiB)
As evident from above output my router assigns IPs via DHCP once authenticated into the Wi-Fi router under standard IP range of 192.168.0.0/24
So under this IP range case, to inspect my small local networkconnected computer I had to run from gnome-terminal or under a /dev/ttyX virtual console:
hipo@noah:~$ nmap -sn 192.168.0.0/24
Starting Nmap 6.00 ( http://nmap.org ) at 2017-09-04 12:45 EEST
Nmap scan report for pcfreak (192.168.0.1)
Host is up (0.011s latency).
Nmap scan report for 192.168.0.103
Host is up (0.00011s latency).
Nmap done: 256 IP addresses (2 hosts up) scanned in 2.53 seconds
-sn argument instructs nmap to do the so called ping scan, e.g. not to do a port s
can after host discovery but just print available hosts that are responding
Some bigger corporate networks are configured to run a couple of local networks simultaneously such as 192.168.168.0.0/24, 192.168.1.0/24, 192.168.2.0/24 etc.
So if that's the case you can add more virtual IPs to your ifconfig after becoming root super user with:
hipo@noah:~$ su root
Password:
root@noah:/home/hipo#
And then run:
/sbin/ifconfig wlan0:0 192.168.1.110 netmask 255.255.255.0
/sbin/ifconfig wlan0:1 192.168.2.110 netmask 255.255.255.0
etc.
Note that here I purposefully choose .110 IP because often the 192.168.1.1 is an IP assigned to the router and that might cause some IP conflicts and trigger alarms in the router security which I want to avoid.
To check just added extra Virtual IPs on wlan0 wireless interface (note that depending on your Wi-Fi card and your driver this interface might come under a different name on your computer):
root@noah# /sbin/ifconfig |grep -i wlan0 -A 1
wlan0 Link encap:Ethernet HWaddr 00:1c:bf:bd:25:59
inet addr:192.168.0.103 Bcast:192.168.0.255 Mask:255.255.255.0
—
wlan0:0 Link encap:Ethernet HWaddr 00:1c:bf:bd:25:59
inet addr:192.168.1.110 Bcast:192.168.1.255 Mask:255.255.255.0
—
wlan0:1 Link encap:Ethernet HWaddr 00:1c:bf:bd:27:59
inet addr:192.168.2.110 Bcast:192.168.2.255 Mask:255.255.255.0
If you're scanning not on your own network but on a public connected network you might prefer to not use the ping scan as this might identify you in router's firewall as possible intruder and could cause you headaches, besides that some network connected nodes are connected to not respond on a ping scan (some networks purposefully disable pings at all) to avoid possibility of the so called ping flood that might overload a router buffer or bring down hosts on the network beinf flooded.
If you have doubts that a network has ping disabled and it shows no result you can give a try to the so called SYN / FIN Stealth packet scan with added requirement to scan for UDP open ports (-sS) argument
root@noah:/~# nmap -sS -sU -sT 192.168.0.1-255
Starting Nmap 6.00 ( http://nmap.org ) at 2017-09-04 13:31 EEST
Nmap scan report for pcfreak (192.168.0.1)
Host is up (0.012s latency).
Not shown: 998 closed ports
PORT STATE SERVICE
80/tcp open http
1900/tcp open upnp
MAC Address: 10:FE:ED:43:CF:0E (Unknown)
Nmap scan report for 192.168.0.100
Host is up (0.0036s latency).
Not shown: 998 closed ports
PORT STATE SERVICE
625/tcp open apple-xsrvr-admin
49153/tcp open unknown
MAC Address: 84:38:35:5F:28:75 (Unknown)
Nmap scan report for 192.168.0.103
Host is up (0.000012s latency).
Not shown: 999 closed ports
PORT STATE SERVICE
22/tcp open ssh
You might also like to add some verbosy (that would generate a lot of output so be careful):
In case if above scan fails due to firewalls and you have a ping scan disabled on the network too you might also try out the so called nmap connect TCP connect scan (-sT), that would avoid the SYN scan. The -sT is useful also if you're not possessing root superprivileges on nmap running host.
nmap -sS -sU 192.168.0.1-255
Note that connect scan could take ages as nmap tries to connect every port from default port scanned ranged on remote found hosts that are reporting as up and running.
If the shown results lead you find some unknown computer / tablet / mobile / phone device connected to your network, then connect to your router and thoroughfully inspect the traffic flowing through it, if you find intruder cut him off and change immediately your router passwords and monitor your network periodically to make sure the unwanted guest did not go back in future.
There is much more you can do with nmap so if you have some extra time and interest into penetration testing I recommend you check out Nmap Book (The Official Nmap project guide to Network Discovery and Security Scanning)